A story in The Hill highlights a “data breach” in the Christian donation site GiveSendGo and how that data breach is being weaponized against people who support the standard of ‘innocent until proven guilty’ in the Wisconsin case against Kyle Rittenhouse. You can read the article HERE, but what I would draw attention toward is not the details of the people being targeted, but rather the process behind the “data breach.”
 We have talked about the weaponization of metadata for several years on this website. Factually we know with certainty that political operatives within the national security apparatus illegally exploit their access to the FBI and NSA database, the totality of all electronic communication, amid Americans.
We have talked about the weaponization of metadata for several years on this website. Factually we know with certainty that political operatives within the national security apparatus illegally exploit their access to the FBI and NSA database, the totality of all electronic communication, amid Americans.
The NSA has made those factual admissions to the FISA court who are supposed to be the backstop to protect the fourth amendment privacy of our nation.
The fact that no-one has ever been held legally accountable for violating the law and extracting the personal information of U.S. citizens shows how eroded the constitutional protections really are. Not a single person has ever been arrested or convicted for exploiting their access… so why would it stop? Short answer: it hasn’t.
As a result every time I read a story that says a “data breach’ is being weaponized for political benefit, my immediate reaction is now to dismiss the oft claimed “hackers” and focus on the most likely source of privacy weaponization: the known and intentional intrusion by government officials and contractors.
 Keep in mind that President Trump granted full declassification authority to AG Bill Barr on May 23, 2019. I would draw your attention to these two paragraphs buried deep in the reporting (emphasis mine):
Keep in mind that President Trump granted full declassification authority to AG Bill Barr on May 23, 2019. I would draw your attention to these two paragraphs buried deep in the reporting (emphasis mine): The New York Times writes a story about John Durham issuing subpoenas to the Brookings Institute for records of Igor Danchenko’s work there. Danchenko was Chris Steele’s primary sub-source for the infamous Steele Dossier.
The New York Times writes a story about John Durham issuing subpoenas to the Brookings Institute for records of Igor Danchenko’s work there. Danchenko was Chris Steele’s primary sub-source for the infamous Steele Dossier. The Big Tech ministry of COVID compliance has again removed scientific discussion that runs counter to the approved narrative presented by the ideological community. In this article we explain why….
The Big Tech ministry of COVID compliance has again removed scientific discussion that runs counter to the approved narrative presented by the ideological community. In this article we explain why….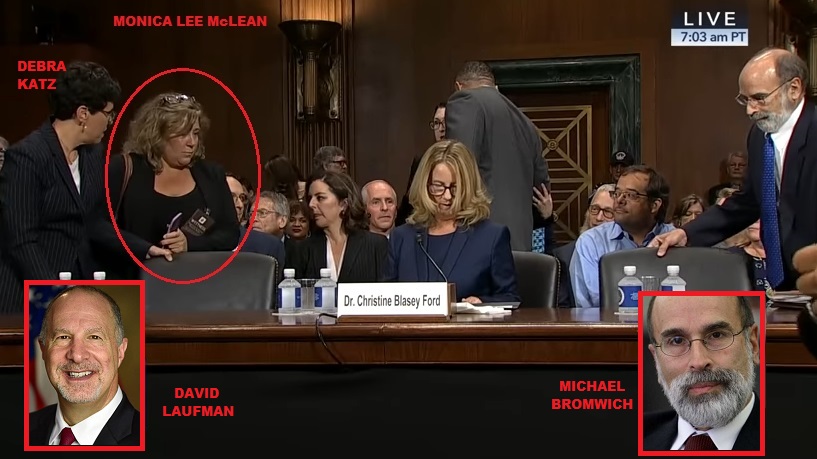
 According to
According to